Our privacy policy is located here.
Manufacturing Solutions
SEE HOW RISK-BASED CYBERSECURITY SERVICES CAN HELP YOU protect what matters most
Your Ultimate Guide to MDR
- Exploring MDR’s history
- Simplifying the need for complex technology
- Fighting cyberattackers with human defenders
- Bringing the ‘R’ to MDR
- Customizing solutions for today and tomorrow
- Understanding your industry
- Tailoring to your needs and budget
Not sure how to get started? Don't wait another minute to reduce your risk of a cyberattack.
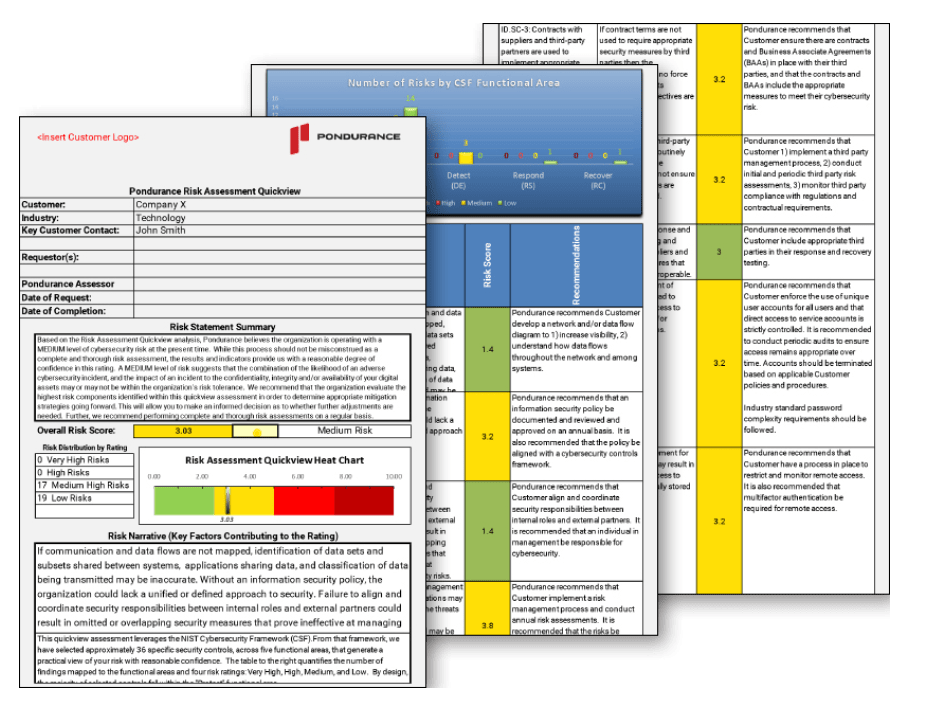
Get started with a risk assessment today
Practical Cybersecurity: A Roadmap for your Manufacturing Organization
Ready to Start the Conversation?
Contact Us to Request a Demo with a Pondurance Expert
Cybersecurity in Manufacturing
The new era of the digital revolution has expanded the frontiers of manufacturing industries, with the convergence of information technology (IT) and operational technology (OT) being central to this transformation. It’s a trend that is rapidly influencing the manufacturing landscape, bringing with it an increased sophistication and efficiency in production operations. However, this digital convergence also expands the attack surface for cybersecurity threats, underlining the critical importance of cybersecurity in manufacturing.
In this realm of interconnected machinery and automated assembly lines, the imperative of “manufacturing plant security procedures” cannot be overstressed. As pacesetters in the Fourth Industrial Revolution, modern manufacturing companies must grapple with the intricate, intertwined network of IT and OT systems. Their security isn’t just a matter of erecting firewalls or installing anti-virus software, it involves a comprehensive approach that appreciates the peculiar risks associated with their systems.
Manufacturing industries continue to be perennial favorites for cyber-criminals due to various reasons. One key reason lies in their use of legacy systems, which often have limited or outdated cybersecurity guardrails. The potent threat of these vulnerabilities has since morphed manufacturing cybersecurity from an optional add-on to an existential necessity.
Manufacturers are often quick to respond to ransomware attacks due to the heavy losses they can incur from operational downtime. This only heightens their attractiveness to would-be attackers, increasing the urgency for strong cybersecurity in manufacturing industry.
In response to these threats, many enterprises are rethinking their tactical approach. Reputable organizations such as Pondurance are increasingly being sought after in the interest of fortifying these manufacturing companies’ cybersecurity defenses, thereby redefining what cybersecurity in manufacturing companies entails.
True to its aptitude for risk-based cybersecurity solutions, Pondurance works by identifying and prioritizing urgent threats, which could otherwise cripple an enterprise’s operations. Their methodology is based on the understanding that the sphere of cybersecurity in manufacturing isn’t static, demanding that they consistently adapt their proactive layers of protection to unforeseen circumstances.
Additionally, the company’s offering of tailor-made cybersecurity solutions is an excellent asset for manufacturers. It guarantees a personalized, robust security architecture that caters to unique business environments and ever-changing threat landscapes. This bespoke approach makes them ideally placed to answer why is cybersecurity important in manufacturing.
In conclusion, the Fourth Industrial Revolution has ushered in a new dawn for the manufacturing sector. However, this promising era brings with it new, intricate cyber threats. The use of inadequate legacy systems and the high likelihood of manufacturers paying ransoms makes them a lucrative target for cybercriminals. It is thus indispensable for manufacturers to bolster their defenses with innovative, risk-based approaches to cybersecurity. With tailored solutions from cybersecurity specialists such as Pondurance, manufacturers can confidently face these digital threats, ensuring they maintain the momentum towards a more interconnected and productive future.
Why is Manufacturing a Target for Cyber Attacks
The evolving cybersecurity landscape poses manifold challenges to myriad industries, yet to precisely comprehend why the manufacturing industry has become a prime target for cyber attacks, we need to delve deep into the convergence of Information Technology (IT) and Operational Technology (OT). This relentless melding of the two distinct branches has expanded the attack surface within the manufacturing industry.
Intricate, complex, and often dated, the manufacturing systems are predominantly driven by legacy systems. Embodied with limited cybersecurity software, these systems operate in an environment of heightened vulnerability. This, coupled with the manufacturing industries’ reliance on continous operations for overall success, makes them a lucrative target for cybercriminals. The mere possibility of production disruption often drives manufacturers into paying hefty ransoms, thereby exacerbating their attractiveness for cyber depredations.
In this context, it’s pivotal to underscore the importance of cybersecurity in the manufacturing industry and the recent surge in outsourcing industry-specific cybersecurity measures to organizations like Pondurance. These experts adopt a risk-based approach to address cybersecurity, enabling manufacturers to focus on their most pressing vulnerabilities while ensuring seamless operational efficiency.
On this front, the advent of manufacturing security standards has been instrumental in thwarting potential cyber threats. They establish a foundational framework designed to protect crucial data and systems, while detecting and managing any prevailing threats. These guidelines fortify the cybersecurity infrastructure, enhancing resilience while fostering a proactive and adaptive cybersecurity management system.
The introduction of cybersecurity measures thus also benefits the supply chain, for any breach in the manufacturing sector can have cascading effects on the entire production network. By securing the manufacturing sector’s digital frontier, one thereby safeguards the entire production ecosystem, ensuring uninterrupted supply and manufacturing continuity. Thus, manufacturers fortify their defense, not out of a compelling obligation but from the driven necessity of securing the future of manufacturing and supply chain operations.
In conclusion, the key to tackling the ever-evolving cyber threat landscape lies in the continual adaptation and reinforcement of cybersecurity practices. Through strategic partnerships with cybersecurity organizations such as Pondurance, manufacturing industries can keep pace with the evolving threats while confidently mitigating vulnerabilities and effectively minimizing potential cyber risks.
Manufacturing Cyber Attacks
Challenges in manufacturing cybersecurity have become a hot topic in recent years. The convergence of Information Technology (IT) and Operational Technology (OT) has unarguably expanded the manufacturing attack surface, making this high-output industry a prime target for increasingly sophisticated cyber threats.
One key reason why the manufacturing sector is so appealing to cybercriminals is its widespread use of legacy systems. These systems, though instrumental in sustaining manufacturing output and operational efficiency, are often ill-equipped with the necessary cyber security software to ward off modern threats. Such vulnerabilities become a magnet for cyber criminals, leaving crucial manufacturing processes under the perpetual shadow of potential disruption.
Furthermore, the importance of continuous operation in this industry makes it more prone to cyber attacks. Manufacturers are often coerced into paying ransomware demands to avoid disruption in their output. This factor makes the industry an attractive target for cyber criminals who leverage the fear of operational cessation to make a quick profit.
Recent years have seen a disturbing rise in these instances of manufacturing cyber attacks. 2022, for instance, has witnessed a spate of new and sophisticated cyber threats targeting the manufacturing sector. These extend from common malware, which intrudes on and disrupts systems, causing downtime and loss of productivity, to silent data breaches where confidential information is surreptitiously accessed and exploited.
Among the spectrum of threats, ransomware has emerged as a prominent cybersecurity risk. It locks down essential systems, and manufacturers—who can ill afford downtime—are often compelled to comply with the cybercriminals’ ransom demands. This distasteful reality is confirmed by recent manufacturing cybersecurity statistics that reveal a worrying prevalence of compliant victims.
Optimistically, in response to such threats, many organizations are now exploring the outsourcing of their cybersecurity needs. Companies like Pondurance, for example, offer a risk-based approach to cybersecurity. They enable manufacturers to prioritize and focus on combating their most pressing vulnerabilities, providing a degree of confidence that’s crucial in this threat-laden landscape.
There have been numerous noteworthy cyber attacks on manufacturers, each offering valuable lessons in cybersecurity. One salient instance was the global WannaCry ransomware attack in May 2017 that hit manufacturing firms hard, paralyzing operations and causing massive losses. These stark episodes underline the urgent need for robust cybersecurity measures in the industry.
Current cyber security statistics paint a landscape riddled with steep challenges. The frequent and high-profile nature of these attacks continues to keep manufacturing cybersecurity challenges at the forefront of discussions within the industry. More than ever, a more robust, anticipatory, and comprehensive approach is required to thwart the evolving nature of Cybercrime in manufacturing.
In conclusion, keeping the manufacturing industry safe from cyber threats is both a monumental challenge and a golden opportunity. While the stakes are undeniably high, the prospect of a safer, more secure industry also offers the potential for unrivaled growth and efficiency. It remains critical, however, to proactively navigate this cybersecurity domain with due diligence to ward off potential cyber threats and ensure sustained, uninterrupted manufacturing output.
What is the Role of Cybersecurity in Manufacturing
The rapid progression of digital technology has introduced smart manufacturing, an innovative development that converges information technology (IT) with operational technology (OT), revolutionizing the manufacturing industry. However, this metamorphosis has equally expanded the attack surface of these industries, rendering them prime targets for cyber threats and security breaches.
The manufacturing industry, traditionally dependent on aging legacy systems, finds itself grappling with limited cybersecurity software and protection. These systems, not originally designed for interconnectedness, offer a ripe opportunity for cyber attackers seeking to infiltrate their networks. Coupled with the ever important need for operational continuity, manufacturers occasionally find themselves left with little choice than to pay demanded ransoms.
There has been an increasing prevalence of varying forms of these nefarious attacks, prompting the industry towards extensive outsourcing of cybersecurity measures. Notable cybersecurity organizations like Pondurance have stepped into this role with chiefly diligence, offering a risk-based approach. This effort aligns manufacturers with expert guidance that focuses on their most pressing software vulnerabilities, bestowing an invaluable confidence within the industry.
Smart manufacturing is defined by its integration of digital technology into the production process, automating operations, improving output, and reducing waste. In this digitized setting, cybersecurity plays a vital role in safeguarding sensitive information, protecting systems and networks, and ensuring the seamless continuity of smart factory operations. The role of “smart factory cyber security” extends beyond mere protection; it strives to ensure proactive measures by early threat detection, mitigation, and ultimately fostering an environment of trust and reliability in the digital landscape of the manufacturing industry.
Related Topics
- Penetration Testing Vs Vulnerability Assessment
- Cybersecurity Compliance Framework
- Cybersecurity Solution
- Cybersecurity For Small Business
- Soc As A Service
- Cybersecurity Compliance
- What Is Penetration Testing
- Nist Cybersecurity
- Cybersecurity Penetration Testing
- Vulnerability Scan
- Cybersecurity Resources
- Cybersecurity Risk Assessment
- Nist Compliance
- Cybersecurity Risk Management
- Cybersecurity Assessment Tool
- Cybersecurity Healthcare
- Cybersecurity Consulting Firms
- Cybersecurity Assessment
- Risk Based Cybersecurity
- Nist Cybersecurity Framework
- How To Prevent Malware Attacks
- Pci Dss
- Cybersecurity Consultant
- Nist Csf
- Penetration Testing Companies