

Shortage of cybersecurity talent
Security professionals are expensive and hard to retain
New compliance and regulation requirements
Undocumented processes in the event of an attack or breach
Security technology is expensive and hard to maintain
Technology alone can't deter motivated attackers
Lack of visibility across the enterprise
Difficulty managing multiple tools and investigating all alerts
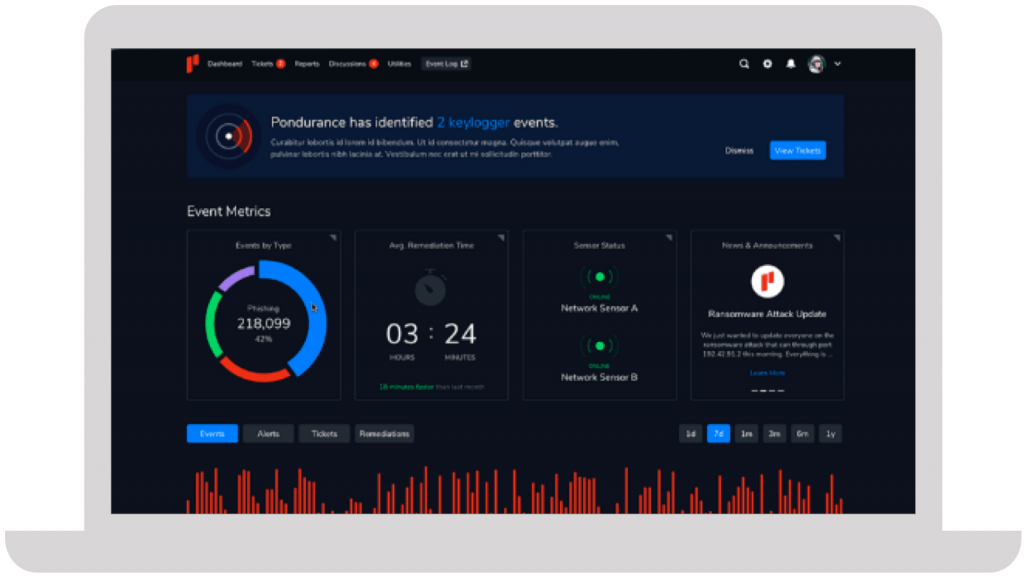
We take a personalized approach to developing your cybersecurity program. Instead of an all-or-nothing approach like other MDR providers, Pondurance lets you pay for what you need, without sacrificing the visibility and transparency you want.
The number of data breaches continues to escalate, putting small businesses on high alert. Nowadays, any information that a business finds valuable is monetizable and a potential target for attack. Learn more in our eBook.
Your company has its own unique set of cyber risks. Though you can’t control the evolving cyber landscape, you can control your cybersecurity strategy. But what’s the best strategic approach to cybersecurity today? Learn more in our eBook.
Join us on-demand to discuss components of MDR and how to choose the right provider for your organization.






They immediately proved their value and earned our trust due to their immense expertise and guidance throughout the entire process.
Steve Long, CEO @ Hancock Health
The realm of technology and network security has rapidly become a significant area of focus for businesses around the world. To combat the ever-evolving threats in this digital age, cybersecurity consulting firms provide an indispensable service to safeguard an organization’s sensitive information. As cyber threats continually evolve, these firms offer tailor-made solutions to secure an organization’s precious data and maintain their credibility.
Cybersecurity consulting firms, such as Pondurance and their highly-rated services, utilize diverse and sophisticated methods to counter cyber threats. On-site assessments, IP address monitoring, data encryption, password protections, and penetration testing are a few examples of the numerous protective measures these professional consulting firms employ.
An organization may need cybersecurity services for a variety of reasons. Cyber threats aren’t exclusive to any specific industry, size, or type of organization. Businesses, regardless of size or sector, are susceptible to these threats, with potentially disastrous consequences. It is imperative for all organizations to understand that graphic data loss, brand degradation, and costly penalties can all result from data breaching. Thus the role of cybersecurity consulting firms has never been more critical. They bolster an organization’s security posture, help devise a resilient contingency plan, and most importantly, implement state-of-the-art defenses to thwart potential cyber attacks.
Among the top cybersecurity consulting firms in the world, Pondurance stands out with its broader, in-depth array of services. Three overarching components define their comprehensive approach. Firstly, they provide digital forensics and incident response, ensuring that in any mishap, the organization can minimize damage and prevent future attacks. Secondly, their managed detection and response service work around the clock to identify and neutralize threats. Lastly, their strategic risk and security advisory service takes a holistic approach to complete cybersecurity including risk assessments, compliance assistance, and cybersecurity training.
When compared with other top-tier cyber security companies, Pondurance provides wider coverage, encompassing not only threat-intelligence but also disaster recovery and resilience. Hence, while evaluating the best cybersecurity consulting firms, organizations must take into account not just protection but also response and recovery features. In this highly sophisticated and unpredictable realm of cybersecurity, firms such as Pondurance emerge as reliable choices, with their all-embracing approach to secure an organization’s digital frontiers.
The world of cyber security has never been as vital and relevant as it is in today’s interconnected globe. The ongoing revolution in digital technology has brought with it unprecedented challenges in maintaining the safety and integrity of online information. To stay ahead in this complex game of tech-based chess, top cybersecurity consulting firms offer essential services designed to shield organizations from relentless cyber threats.
Among the top dogs in this field resides a plethora of cybersecurity consultants with their unique proficiencies and resources. These cyber security consulting companies offer a wide range of services from threat assessments, penetration testing, to compliance support, providing organizations with a robust security posture.
Positioned at the pinnacle in this industry is Pondurance, a firm heavily recognized in the United States and worldwide. Pondurance has etched its name amongst the top cybersecurity consulting firms in the world and the USA. They offer a suite of services, from threat hunting to incident response, ensuring their clients have the highest level of security measures in place.
When debating the top cybersecurity consulting firms, compensation is an intriguing part to ponder about. The cyber security consulting salary reflects the importance of this role in safeguarding organizations. Highly educated professionals who excel at identifying vulnerabilities, constructing secure networks, and advising on best practices command equally loft compensation.
Physical security consulting firms also play a critical role in safeguarding businesses. A holistic security strategy includes both cybersecurity and physical security, as breaches often occur due to physical vulnerabilities. Top physical security consulting firms provide in-depth threat assessments, security camera placement strategies, and employee access control systems to name but a few of their services.
Expanding the geographical focus to Florida, one finds a number of top-notch cybersecurity consulting firms. Names such as Pondurance, among others, have established their presence in this region. Their offerings evolve as organizations’ security needs deepen, providing not only protection but also comprehensive solutions tailored to each client’s specific needs.
Florida, especially around Tampa, is home to a significant number of both large and small cybersecurity companies. These cybersecurity consulting firms near Tampa, FL offer services ranging from tactical security defenses to strategic planning and implementation of security measures. Tactics include network security, cloud computing security, and advanced threat detection, ensuring organizations in the area are fully protected.
In the end, the clear line drawn through these diverse elements is the accelerating need for top cybersecurity professionals. From the towering skyscrapers of global organizations to the bustling enterprises in Florida, these professionals work diligently to secure sensitive information in a world where cyber threats are continually evolving. Investing in these top cybersecurity consulting firms is an intelligent move, one that provides peace of mind in an unpredictable digital world.
In today’s digital landscape, cybersecurity threats pose an existential challenge to organizations across sectors, necessitating robust and proactive solutions. Private, public, and nonprofit entities alike recognize the imperative need to navigate the choppy cyber waves effectively, often turning to cybersecurity advisory services for expert guidance.
Cybersecurity consulting companies, specializing in a wide array of services, play a pivotal role in bolstering the digital resilience of organizations. From proactive measures like vulnerability assessments to reactive approaches such as incident response advisories, these firms contribute significantly to fortifying cybersecurity defenses.
Among the top cybersecurity consulting firms in the USA, Pondurance shines as a beacon of excellence. Renowned for its prolific risk reduction strategies and commitment to holistic cyber hygiene, Pondurance is synonymous with cybersecurity excellence, providing invaluable support to its clients.
Moreover, cybersecurity consulting extends beyond the digital realm to address physical security concerns. By conducting exhaustive reviews of physical access controls, intrusion detection systems, and video surveillance, these firms ensure comprehensive security measures across both digital and physical domains.
Application security testing is another critical service offered by cybersecurity consultants, focusing on identifying and remedying vulnerabilities in software applications to safeguard against unauthorized access.
In the legal sphere, cybersecurity consultants provide invaluable support by navigating complex data breach regulations and offering advice on regulatory compliance to prevent breaches proactively.
Cybersecurity compliance is yet another essential aspect of advisory services, given the multitude of cybersecurity regulations worldwide. Consultants perform audits, evaluations, and provide recommendations to ensure organizations not only meet but exceed compliance standards.
In conclusion, cybersecurity advisory services offered by top firms like Pondurance serve as indispensable allies in combating invisible threats in today’s digital landscape. By partnering with the right consulting firm and implementing dedicated in-house measures, organizations can effectively conquer the omnipresent digital challenges they face.
Risk-based cybersecurity, an approach that prioritizes defense efforts based on their potential impact, is a necessary component in today’s world where threats constantly evolve. It essentially involves understanding and evaluating the risks associated with different assets, thus allowing an organization to efficiently use the resources at its disposal and better protect against cyber threats.
One of the critical strategies of risk-based cybersecurity entails cyber risk assessment, a process that helps in identifying and prioritizing potential vulnerabilities in a network. This involves analyzing the various cyber vulnerabilities based on their probability of occurrence as well as their potential impact on the organization’s operations. By conducting a comprehensive cyber risk assessment, a firm can gain an insight into its overall cybersecurity posture, allowing it to address any weaknesses and enhance its defenses accordingly.
An integral part of a robust risk-based cybersecurity strategy is vulnerability management. Efficient vulnerability management ensures an organization continually assesses, treats, and eliminates both potential and ongoing cyber threats. Regularly monitoring for risks helps firms identify the weak points in their security infrastructure and prioritize their resources to address the most significant threats.
Managed detection and response (MDR) is a cybersecurity service provided by consulting firms, such as Pondurance, one of the top-tier security organizations. MDR providers facilitate the detection of cyber threats, implementing rapid response measures to limit any damage inflicted. Pondurance, in particular, provides its clients with a risk-based approach to cybersecurity including monitoring, detection, threat hunting, and response services, all tailored to the organization’s specific needs.
Furthermore, threat hunting cybersecurity is an advanced component of risk-based cybersecurity. This proactive approach involves analyzing networks for potential threats that could have already infiltrated a network, hence minimizing their impact. Pondurance’s threat hunters utilize advanced techniques to identify and neutralize potential threats before they cause significant harm or damage.
In sum, one of the paramount reasons for requiring cybersecurity consulting services would be their unmatched expertise in implementing risk-based cybersecurity programs. Firms like Pondurance have the technical skill and strategic insights to design and implement comprehensive cybersecurity strategies, assisting organizations in prioritizing areas of high risk, continuously monitoring for threats, and responding swiftly and effectively when breaches occur. It’s a crucial investment that could mean the difference between staying safe and suffering a potentially devastating cyber attack.a