

Shortage of cybersecurity talent
Security professionals are expensive and hard to retain
New compliance and regulation requirements
Undocumented processes in the event of an attack or breach
Security technology is expensive and hard to maintain
Technology alone can't deter motivated attackers
Lack of visibility across the enterprise
Difficulty managing multiple tools and investigating all alerts
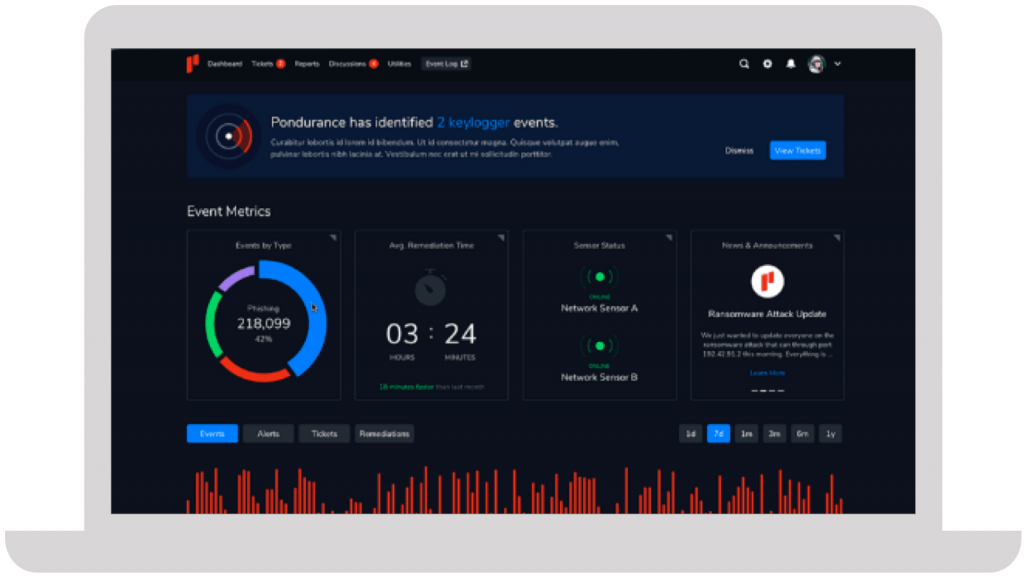
We take a personalized approach to developing your cybersecurity program. Instead of an all-or-nothing approach like other MDR providers, Pondurance lets you pay for what you need, without sacrificing the visibility and transparency you want.
The number of data breaches continues to escalate, putting small businesses on high alert. Nowadays, any information that a business finds valuable is monetizable and a potential target for attack. Learn more in our eBook.
Your company has its own unique set of cyber risks. Though you can’t control the evolving cyber landscape, you can control your cybersecurity strategy. But what’s the best strategic approach to cybersecurity today? Learn more in our eBook.
Join us on-demand to discuss components of MDR and how to choose the right provider for your organization.






They immediately proved their value and earned our trust due to their immense expertise and guidance throughout the entire process.
Steve Long, CEO @ Hancock Health
Cybersecurity solutions have become essential for modern businesses, especially small companies that lack resources and expertise to protect their valuable data and systems. At Pondurance, we deliver world-class managed detection and response services because we understand the critical importance of cybersecurity. With cyber threats evolving at an alarming pace, organizations of all sizes and industries are at risk. That’s why cybersecurity solution services are crucial to ensure businesses stay protected from potential attacks.
One important aspect of a robust cybersecurity solution is understanding the different types of cybersecurity measures available. Some common types include:
* Firewalls
* Anti-malware software
* Breach detection systems
* Encryption tools
* Employee training programs
Each of these components plays a crucial role in safeguarding an organization’s digital assets and preventing unauthorized access to sensitive information. Implementing cybersecurity solutions offers numerous advantages that contribute to a company’s success. For instance, robust information security solutions can improve customer trust by safeguarding personal data, leading to increased customer satisfaction, improved brand reputation, and better financial performance.
Investing in cybersecurity is particularly important for small businesses with limited resources. These companies often face unique challenges when addressing cyber risks. However, in leveraging professional cybersecurity solution services, they can navigate these challenges successfully.
Implementing practical solutions to cybersecurity threats also involves staying up-to-date on the latest trends and developments within the field. This includes continually evaluating current processes and technologies used within an IT infrastructure while remaining vigilant against emerging dangers that may pose new risks.
In conclusion, the increasing complexity of today’s digital landscape and the prevalence of sophisticated cyber attacks make information security solutions more crucial than ever. By using various types of cybersecurity measures, businesses can stay protected and thrive in an increasingly competitive marketplace.
Mitigating security threats is an essential practice for every business. Organizations can no longer ignore the potential risks and damages associated with cyber attacks. To safeguard against such threats, businesses must:
Threat hunting means actively searching for signs of malicious activity within an organization’s network that may not have been detected by traditional security measures. By proactively identifying and mitigating threats, businesses can prevent attacks from escalating.
Effective threat hunting requires skilled personnel with expertise in cybersecurity and advanced tools, such as artificial intelligence (AI) and machine learning algorithms, that can analyze large amounts of data quickly and accurately.
To prevent security threats from escalating into devastating cyber attacks, businesses must adopt a multi-layered approach to their cybersecurity strategy. This includes:
In addition to implementing these measures, organizations should adhere to cybersecurity best practices for business operations, which include:
Another crucial aspect of mitigating security threats is educating employees about how to prevent cyber attacks. Employees are often considered the weakest link in any cybersecurity posture due to human error or lack of awareness about potential threats. Providing ongoing education on safe online habits, such as avoiding suspicious email attachments, creating strong passwords, and never sharing sensitive information through unsecured channels, can significantly reduce the risk of cyber attacks originating from within the organization.
To summarize, mitigating security threats requires a proactive and multi-faceted approach that encompasses threat hunting, adherence to cybersecurity best practices for business operations, and thorough employee education on preventing cyber attacks. By implementing these strategies, organizations can significantly reduce their vulnerability to cyber threats and maintain the integrity of their data and systems.
Managed detection and response (MDR) is a rapidly growing area of cybersecurity that focuses on the proactive identification, containment, and remediation of threats. By combining advanced technology with human expertise, MDR services provide organizations with the tools to detect and respond to cyber threats in real time.
During MDR, skilled analysts use advanced techniques, such as machine learning, behavioral analysis, and anomaly detection, to identify patterns indicative of malicious activity. After identifying potential threats, an MDR team works quickly to:
To further enhance an organization’s security posture, many businesses choose to partner with an MDR consultant. These experts possess a deep understanding of both current and emerging threats, as well as best practices in cybersecurity management.
At Pondurance, we specialize in MDR and provide preemptive cybersecurity solutions that:
In today’s increasingly connected world, managed detection and response services are more critical than ever in protecting sensitive information from cybercriminals. With the innovative application of advanced analytics, threat hunting and response capabilities, and tailored advice from MDR consultants, organizations can effectively guard against even the most sophisticated cyber attacks.
Incident response is a critical aspect of any organization’s cybersecurity strategy. It refers to the process of identifying, investigating, and addressing potential security threats or breaches in a systematic manner.
Having an effective incident response plan is essential for protecting valuable data and maintaining business operations. An incident response plan is a well-documented set of policies and procedures outlining how an organization will handle various types of cyber incidents. This helps organizations minimize the damage caused by cyber attacks and reduce the overall risk associated with such incidents.
The primary goal of cyber incident response is to quickly identify and resolve any ongoing threats to an organization’s information systems. This may involve coordinating efforts between various internal teams, such as IT departments, legal counsel, and public relations specialists, as well as external partners, like law enforcement agencies or third-party cybersecurity experts. The ability to identify potential security risks and take appropriate action is crucial in minimizing the impact of a breach on an organization’s reputation and bottom line.
When planning for incident response, organizations should invest in cyber insurance. This specialized type of insurance coverage helps businesses and individuals mitigate financial losses resulting from cyber-related incidents, such as data breaches, ransomware attacks, and other cyber threats. It typically covers expenses related to incident response, legal fees, notification costs, and potential liability claims, providing a crucial safeguard against the financial impact of cyber attacks.
To ensure optimal results when dealing with cybersecurity incidents, many organizations enlist the services of a Digital Forensics and Incident Response or DFIR consultant. These professionals specialize in helping businesses investigate digital evidence associated with security breaches while providing expert guidance on the remediation steps required for recovering from such events. Pondurance specializes in cybersecurity incident response to prevent future incidents and minimize losses.
To sum up, incident response is a vital component of any organization’s cybersecurity framework. By implementing robust incident response plans and engaging the expertise of specialized consultants, organizations can reduce the risks and damage associated with security breaches and protect themselves against future threats.
Vulnerability management protection helps organizations maintain the integrity and security of their information systems. This comprehensive approach to identifying, assessing, and mitigating potential weaknesses in an infrastructure prevents unauthorized access or damage to valuable data and information.
One essential component of vulnerability management protection is the practice of penetration testing versus vulnerability assessment:
Penetration testing involves simulating real-world cyber attacks on an organization’s network or systems to identify potential vulnerabilities that could be exploited by malicious actors.
Vulnerability assessments typically involve a more passive analysis of an infrastructure using automated scanning tools to detect known vulnerabilities.
Both approaches are vital for ensuring comprehensive coverage against potential threats. However, they must be used in conjunction with one another as part of a broader vulnerability management program.
In addition to implementing these key techniques, businesses may also choose to engage professional vulnerability management services to help bolster their internal security efforts. These specialized service providers can provide expert guidance and support throughout the entire lifecycle of a vulnerability management program, from initial assessment and prioritization through remediation and ongoing monitoring. By partnering with an expert like Pondurance, organizations can benefit from extensive resources dedicated solely to information security.
In summary, a well-rounded vulnerability management program should combine rigorous penetration testing and thorough vulnerability assessments with specialized experts. Investing in robust vulnerability management protection will minimize risk and help secure an organization’s reputation for years to come.
Cybersecurity is an ever-evolving landscape, with new threats emerging daily. In such a high-stakes environment, organizations must enlist the help of cybersecurity advisory services, like Pondurance, which provide expert advice and guidance on the most effective strategies to safeguard their digital assets. These services may also include cybersecurity penetration testing.
A critical aspect of effective cybersecurity practices is the role played by the cybersecurity solution architect. These professionals possess both technical expertise and strategic vision, enabling them to design and develop comprehensive security solutions tailored to an organization’s unique needs. A cybersecurity solution architect will:
* Evaluate existing infrastructure
* Assess potential risks
* Recommend suitable technology investments
* Oversee implementation
* Stay up to date with the latest trends and developments in the field of cyber defense
An application security consultant provides additional support for securing software applications. They are familiar with coding best practices, common vulnerabilities, and relevant regulatory compliance requirements. They can also conduct thorough assessments of an organization’s applications to detect possible flaws that hackers could exploit.
A dedicated cybersecurity consultant brings technical acumen, deep industry knowledge, and strategic insight to the table. With a clear understanding of business operations and objectives, they can advise on holistic security solutions to mitigate risk while supporting long-term organizational growth.
In conclusion, safeguarding valuable data assets and maintaining the integrity of digital infrastructure is an increasingly complex challenge. By partnering with knowledgeable professionals who offer cybersecurity advisory services, organizations can access specialized skills, such as cybersecurity testing, and successfully navigate this landscape.