

Shortage of cybersecurity talent
Security professionals are expensive and hard to retain
New compliance and regulation requirements
Undocumented processes in the event of an attack or breach
Security technology is expensive and hard to maintain
Technology alone can't deter motivated attackers
Lack of visibility across the enterprise
Difficulty managing multiple tools and investigating all alerts
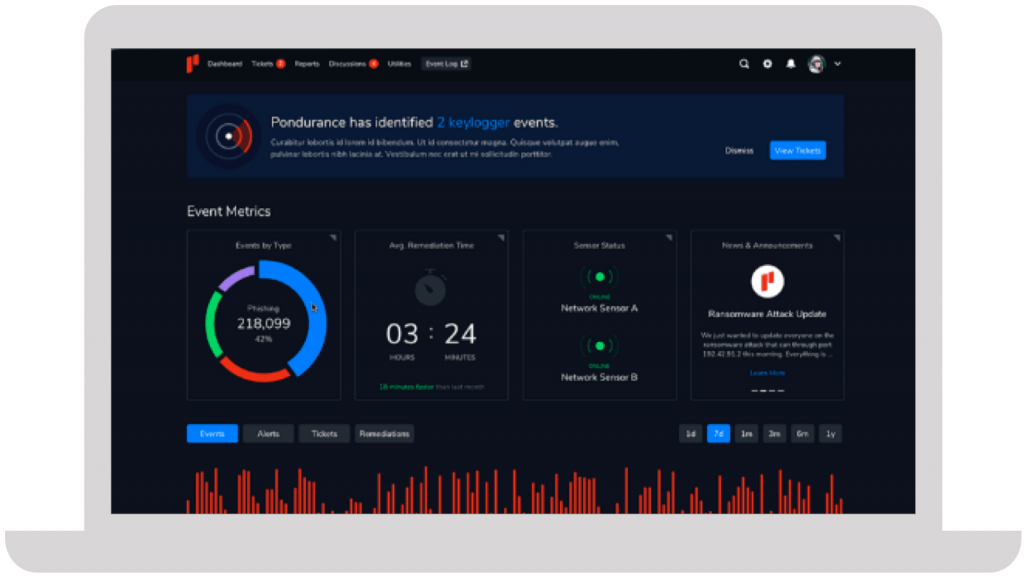
We take a personalized approach to developing your cybersecurity program. Instead of an all-or-nothing approach like other MDR providers, Pondurance lets you pay for what you need, without sacrificing the visibility and transparency you want.
The number of data breaches continues to escalate, putting small businesses on high alert. Nowadays, any information that a business finds valuable is monetizable and a potential target for attack. Learn more in our eBook.
Your company has its own unique set of cyber risks. Though you can’t control the evolving cyber landscape, you can control your cybersecurity strategy. But what’s the best strategic approach to cybersecurity today? Learn more in our eBook.
Join us on-demand to discuss components of MDR and how to choose the right provider for your organization.






They immediately proved their value and earned our trust due to their immense expertise and guidance throughout the entire process.
Steve Long, CEO @ Hancock Health
Artificial Intelligence (AI) and Cyber security go hand in hand.
The substantial rise in cybercrime in the past few years has generated a tremendous market for artificial intelligence (AI)-driven cybersecurity products. The global AI market totaled $428 billion in 2022 and is expected to surge to more than $2 trillion by 2030, according to Fortune Business Insights. The introduction of ChatGPT, the OpenAI tool that can write stories, solve math equations, and program code, showed the enthusiasm and rapid adoption of AI among corporations and individuals. ChatGPT launched in November 2022 and, in just two months, set a record as the fastest app ever to reach 100 million active users.
Decision-makers may want to believe that they can execute AI for their networks to solve all their cybersecurity problems, but that’s not the reality. Cybersecurity experts currently use AI and automation to detect and respond to cyber threats. But using technology alone is not enough. Human attackers must be confronted by human defenders, making people the most important component of any comprehensive cybersecurity program.
Artificial intelligence plays a significant role in cybersecurity. It is used to enhance security measures and defend against cyber threats. AI-powered systems can analyze vast amounts of data to detect anomalies, identify patterns, and predict potential cyber-attacks. Additionally, AI helps in automating threat detection, response, and mitigation processes, making it easier for cybersecurity professionals to handle complex and sophisticated threats. And those are the key words, “making it easier for cybersecurity professionals to handle the threats”.
The upside and downside of artificial intelligence and cybersecurity is the vast amount of data AI can process and unfortunately, the vast amount of AI generated false positives and negatives it can produce. With every flagging of legitimate activities as a threat or each time AI Cybersecurity fails to detect actual cyber threats, leads to reduced trust in the system.
And don’t forget it is essential to ensure that AI itself is secure to prevent adversaries from exploiting AI systems for malicious purposes. AI algorithms can become targets of attack as adversaries work to manipulate or exploit AI systems by feeding them malicious data.
But perhaps the biggest downside of AI cybersecurity is the same downside for every cybersecurity technology, the overreliance on the technology (AI or not). Relying solely on any technology and in particular the shiny new AI technology for cybersecurity can create a false sense of security. Human oversight and expertise are still critical for comprehensive cybersecurity protection. Ask ChatGPT about the downside of AI and Cybersecurity and it too will spit out a response that includes “Dependency and Overreliance” as one of the key challenges.
The field of AI in cybersecurity continues to evolve as both attackers and defenders employ advanced techniques in their efforts. Without the skilled work of humans to properly configure cybersecurity software, and fine tune the systems, attackers can find new ways to break the systems and false positives can quickly fatigue the team, making it hard to find the true threats. Without the consistent work of humans to understand the context and apply learnings, AI cybersecurity is nothing more than an “alert factory” alerting on everything. You simply can’t take the Human out of cybersecurity.
And too much cybersecurity focused on artificial intelligence alone, can lead to too much tightening of controls which can frustrate the business users and customers. While controls are essential, AI cybersecurity learned controls, if not managed with human intelligence, can add unnecessary complexity and friction, into the user experience. Limiting employee access, and the use of certain software and tools can hinder employee productivity, while slow response times can be particularly frustrating for employees and customers. Finding the right balance of cybersecurity and business processes has been a mandate for cybersecurity professionals and business owners. Now with AI cybersecurity, the cybersecurity professional needs to continue to balance controls. It is the balance of artificial intelligence and human intelligence that protects businesses from cyberattacks and keeps the business moving forward.
Just as cybersecurity professionals are using AI to defend against cyberattacks, cybercriminals are using AI to launch cyberattacks. Using AI, they may employ any number of innovative ways to infiltrate a network. They could design malware signatures that can evade traditional security measures and that would constantly change to avoid detection by firewalls. AI can analyze massive amounts of public data to create highly sophisticated phishing emails and spear phishing attacks to fool victims into clicking on them, or even use deepfake audio technology to impersonate the voice of a co-worker. AI-driven chatbots or virtual agents do a great job of mimicking human interactions, making all types of social engineering attacks more convincing and much harder to detect. Since many of these AI-driven tactics would be new means of attack on a network, AI alone would not have the learning or logic required to identify these attack methods. Such evolving threats would require human expertise.
And there are other ways artificial intelligence has been leveraged by bad actors to enhance their methods of attack. Attackers can manipulate data to bias models and cause them to make bad decisions and attackers can even use AI generated examples to fool AI and cybersecurity systems to gain access to networks.
While cyber criminals are using AI-generated cyber-attack methods, cybersecurity professionals are also using AI and machine learning to develop advanced threat detection, as well as prevention and response solutions. AI cybersecurity tools have extended the battel between human attackers and human defenders.
When detecting and responding to an attack, human experts have definite advantages that AI and cybersecurity technology alone does not have. Consider a ransomware attack, for instance. Ransomware is considered the greatest threat to endpoint security, with zero-day exploits, distributed denial-of-service attacks, credential theft, and distribution point sprawl also ranking as high-priority cybersecurity concerns for organizations. A human can identify malicious code and warning signs, distinguish false positives from alerts, and understand the context, relevance, and attack motivation of the cybercriminal in ways technology can’t. To protect your organization, you need to combat ransomware with the right balance of human defenders and technology.
It is critical that artificial intelligence cybersecurity is not considered a replacement for the expertise of a cybersecurity professional for other reasons like data privacy. Many AI cybersecurity solutions require access to sensitive data and the protection of that data is critical to avoid potential breaches. For example, AI models like ChatGPT warn against any confidential information being shared with any AI models like ChatGPT due to security and privacy risks
Like any cybersecurity technology, as AI and cybersecurity become more prevalent, human cyber criminals will develop tactics to break down AI-powered defenses. Cybercriminals take bold steps to gain access to networks, and these methods can sometimes bypass established technology. In some cases, even an EDR solution will not detect the malicious activity from the threat actor, therefore a human response is needed.
And human intelligence is needed to feed the innovation in AI cybersecurity solutions. Yet another reason why AI and cybersecurity should not be a standalone solution, but part of a complementary cybersecurity effort with human expertise.
Technology research and consulting firm Gartner now recommends humans as well. The firm suggests that organizations “use MDR services to obtain 24/7, remotely delivered, human-led security operations capabilities when there are no existing internal capabilities, or when the organization needs to accelerate or augment existing security operations capabilities.” That way, an organization can have access to human analysts, threat responders, and security experts who can function as a cybersecurity team or extended team to provide dynamic detection and prevention controls.
Of course, humans working hand in hand with advanced technology is the best cybersecurity protection against cyber threats. In particular, the team should work with technology that ensures 360-degree visibility across all networks, endpoints, logs, and clouds for 24/7 comprehensive monitoring and detection of malicious activity.
AI cybersecurity is a vital component in safeguarding networks and sensitive data. Leveraging AI’s intelligence and automation capabilities, organizations can proactively defend against cyber threats. However, the human factor remains integral in harnessing the full potential of AI-driven solutions. By embracing the synergy between human and AI defenders, businesses can establish a formidable cybersecurity defense, ensuring a secure digital future.
Technology alone isn’t enough to keep your organization safe from cybercriminals. Human attackers must be confronted by human defenders. When looking for a partner to help you mature your Cybersecurity, be sure to ask about the people, process, and technology your partner uses and be particularly interested in their adoption of AI Cybersecurity tools. Make sure your organization has the humans and technology it needs to protect against a cyberattack.
In an era where cyber threats are becoming more complex and sophisticated, Pondurance has extensive experience with AI cybersecurity, providing the organizations they support with the expertise needed to navigate the complex and ever-evolving cyber threat landscape. Through our proactive approach, customer-centric focus, and commitment to continuous innovation, Pondurance has helped businesses of all sizes achieve a heightened level of cybersecurity resilience. As cyber threats continue to evolve, Pondurance stands ready to support and defend its clients, ensuring a secure digital future for all.
Read more about choosing and cybersecurity provider (hyperlink to eBook) and questions to ask your provider.
The Human Element: The Key to a Successful Cybersecurity Strategy
Combat Ransomware with the Right Balance of Human Defenders and Technology
AI Alone Is Not the Answer to Cybersecurity; Humans Are Needed
Humans & Tech: Defending Against Cyberattacks With Technology and Human Expertise
https://venturebeat.com/security/how-combining-human-expertise-and-ai-stop-cyberattacks/
Pondurance MDR: Cybersecurity Backed By Authentic Human Intelligence
Human vs. Tech: Why You Need Both to Defend Against Ransomware