

The number of data breaches continues to escalate, putting small businesses on high alert. Nowadays, any information that a business finds valuable is monetizable and a potential target for attack. Learn more in our eBook.
Your company has its own unique set of cyber risks. Though you can’t control the evolving cyber landscape, you can control your cybersecurity strategy. But what’s the best strategic approach to cybersecurity today? Learn more in our eBook.
Join us on-demand to discuss components of MDR and how to choose the right provider for your organization.
Shortage of cybersecurity talent
Security professionals are expensive and hard to retain
New compliance and regulation requirements
Undocumented processes in the event of an attack or breach
Security technology is expensive and hard to maintain
Technology alone can't deter motivated attackers
Lack of visibility across the enterprise
Difficulty managing multiple tools and investigating all alerts
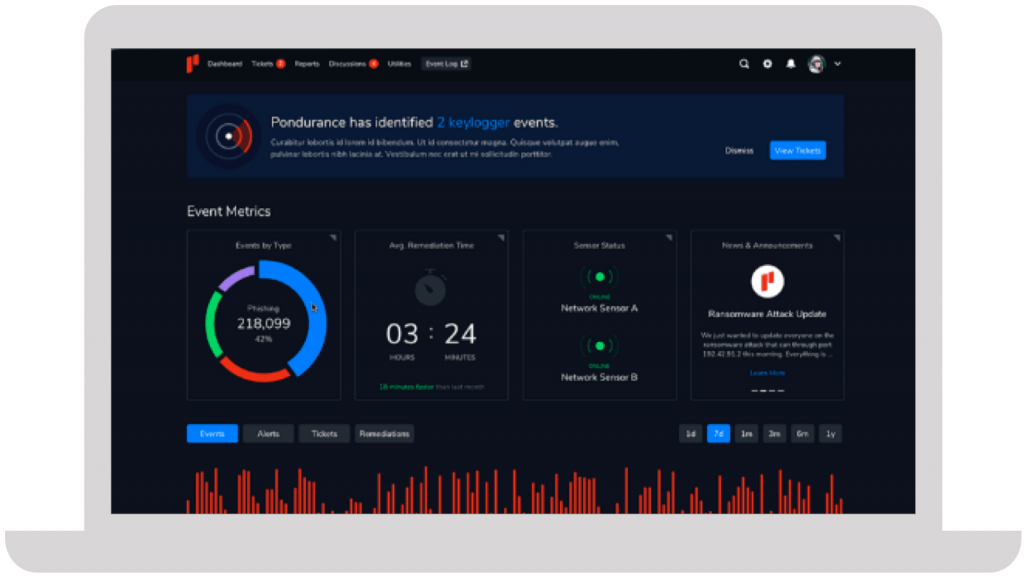
We take a personalized approach to developing your cybersecurity program. Instead of an all-or-nothing approach like other MDR providers, Pondurance lets you pay for what you need, without sacrificing the visibility and transparency you want.






They immediately proved their value and earned our trust due to their immense expertise and guidance throughout the entire process.
Steve Long, CEO @ Hancock Health
In today’s rapidly evolving technological landscape, the significance of robust cybersecurity measures cannot be overstated, especially for enterprises. With the increasing complexity of technology, cybersecurity companies are instrumental in devising comprehensive strategies to mitigate cyber risk and ensure informed security for organizations. These top cybersecurity companies assist security teams in conducting thorough cyber threat assessments and implementing effective threat intelligence solutions to safeguard sensitive data and information systems.
A well-crafted cyber risk management strategy is essential for organizations to anticipate and mitigate potential impacts of cyber threats and data breaches. By conducting regular risk assessments and implementing vulnerability management practices, businesses can enhance their security posture and effectively manage potential threats to their information systems.
One of the critical components of a cybersecurity strategy is the establishment of a Security Operations Centre (SOC), where skilled professionals utilize advanced technologies to detect and respond to cybersecurity incidents promptly. Additionally, compliance initiatives, such as adhering to the NIST cybersecurity standard, are crucial for maintaining regulatory compliance and avoiding legal issues.
In the event of a cyber breach or attack, having a robust incident response plan is vital for minimizing loss and damage to the organization while maintaining trust with customers and clients. Managed services offered by cybersecurity companies like Pondurance can play a pivotal role in proactively monitoring networks, detecting potential threats, and swiftly responding to security breaches.
Anticipating future cyber threats and continuously updating cybersecurity strategies is imperative in this dynamic landscape. Therefore, organizations must adopt a multi-layered and adaptive approach to cybersecurity to effectively safeguard against evolving cyber threats and ensure the protection of sensitive data.
A comprehensive cyber security strategy is crucial in today’s digital landscape. By firmly addressing and neutralizing the rising threats and potential breaches, businesses can protect their data and continue to operate without fear. The components of a cyber security strategy often encompass various elements, including a cyber security strategy document, a cyber security strategy framework, an incident response plan, and the implementation of a security operations center (SOC), amongst others.
Developing a robust cyber security strategy document is one of the first key steps in formulating a strong defense. This document not only identifies potential risk areas but also lays forward plans to mitigate them. It strategically aligns the organization’s security initiatives with its overarching vision and objectives.
Once the cyber security strategy document is in place, the next layer of defense is the cyber security strategy framework. A well articulated framework helps to comprehensively interpret and implement the guidelines laid out in the strategy document. The NIST CSF or the National Institute of Standards and Technology Cybersecurity Framework is a wonderful exemplar in this regard. Being risk-based, it allows organizations to customize their defense strategy according to specific requirements, creating a contextual, proactive approach.
Incident response planning forms another significant chunk of a comprehensive cyber security strategy. When a breach or an attack occurs, it’s crucial to have a predetermined, fast-paced action plan in place. An incident response plan can contain, eradicate, and recover from an incident, minimizing damages and downtime.
On top of these, having a Security Operations Center enhances the cyber security posture of an organization immeasurably. A SOC centralizes the organization’s security responsibilities into one division, proving instrumental in threat management and incident response. To solidify it further, organizations can opt for SOC as a service, where a third party takes on the responsibility of maintaining the SOC, thereby ensuring continuous security monitoring and management.
Cybersecurity risk management, an integral part of the strategy, is about identifying, assessing, and prioritizing risks to the organization’s information assets. Using a risk-based approach ensures that resources are allocated appropriately to tackle the most pressing threats.
As a leader in this realm, Pondurance takes these integral components to a new paradigm. Pondurance not only offers the components but also ensures expert service offerings in all these areas, through its comprehensive security and compliance solutions. With a focus on a robust cyber security strategy, Pondurance is instrumental in helping businesses tackle the complex cyber security landscapes with efficiency, dexterity, and sophistication.
In the dynamic landscape of digital trade and exchange, cybersecurity companies play a pivotal role in shaping the security posture of organizations. Top cybersecurity companies like Pondurance excel in devising comprehensive cybersecurity policies that encompass critical elements such as Security Operations Center (SOC) services, compliance initiatives, incident response plans, and managed services. These companies are at the forefront of addressing evolving cyber threats and ensuring the resilience of businesses in the face of digital challenges.
Furthermore, cyber risk management is a cornerstone of any effective cybersecurity strategy. By identifying, assessing, and prioritizing risks to information assets, organizations can allocate resources efficiently and proactively mitigate potential threats. Cybersecurity companies provide invaluable expertise in this area, offering tailored solutions to address the unique risk profiles of different organizations.
Informed security is another key aspect emphasized by cybersecurity companies. Through threat intelligence and cyber threat assessments, these companies equip security teams with the knowledge and tools needed to stay ahead of potential threats. By staying informed about emerging cybersecurity threats and vulnerabilities, organizations can strengthen their defenses and minimize the likelihood of successful cyber attacks.
Moreover, cybersecurity companies play a crucial role in incident response planning, helping organizations develop robust strategies to contain and mitigate the impact of cyber breaches. With their expertise in managing security incidents, these companies enable organizations to respond swiftly and effectively to cyber threats, minimizing disruption to business operations and preserving the integrity of sensitive data.
In conclusion, cybersecurity companies are essential partners in the ongoing battle against cyber threats. By providing comprehensive cybersecurity solutions, expert guidance, and proactive risk management strategies, these companies empower organizations to navigate the complex digital landscape with confidence and resilience.
The unforgiving world of digital trade and exchange mandates thorough, rigorous, and meticulously tight security measures. Amid an onslaught of cyber threats, the emphasis falls on an organization’s preparedness, outlined in their comprehensive cybersecurity strategy. It is in this area where Pondurance proves its mettle, standing as a formidable leader in devising comprehensive cybersecurity policies that envelop Security Operations Center (SOC), compliance initiatives, incident response plans, and managed services.
A critical facet of cybersecurity is ensuring compliance with industry standards. Businesses across various industries face different types of threats, and consequently, different compliance guidelines are established to cater to these unique needs. This is where the relevance of cybersecurity compliance rings true. Whether your business environment obliges you to adhere to NIST compliance or demands strict CMMC guidelines, compliance not only assures your business safety but also demonstrates responsibility and commitment to your customers and stakeholders.
NIST compliance offers a benchmark in cyber hygiene, codifying security measures necessary to minimize the occurrence and impact of cyber events. This widely accepted standard of practice lays out a proactive strategy to identify and prioritize threats. Pondurance’s consulting services offer expert guidance in designing and implementing NIST-compliant protocols, thereby reducing risk and enhancing security postures.
Similarly, CMMC establishes a base for organizations dealing with Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). As cyber threats evolve, so does CMMC standards, making it imperative for businesses to stay updated and compliant. Pondurance, with its expert guidance and advanced tools, aids in achieving and maintaining CMMC compliance, hence fostering trust among stakeholders, including federal government agencies.
The importance of achieving cyber compliance cuts across industries, urging the necessity for PCI DSS compliance within the e-commerce sector. With increase in online transactions, protecting cardholder data becomes paramount. Pondurance’s PCI DSS compliance assistance ensures secure handling of this data, thereby protecting businesses from facing costly penalties while imbuing customer trust.
When considering the sensitive nature of health data, HIPAA compliance emerges as an industry requirement for healthcare providers. Pondurance’s expertise extends to this sector as well, offering guidance and solutions tailored to adhere to HIPAA regulations, protecting patient data, and preventing breaches that could lead to devastating fines and loss of reputation.
Cybersecurity compliance isn’t just a box to be checked. It’s an ongoing, evolving process. Pondurance excels in providing expert consulting services tailored to an organization’s specific requirements, helping them realize the complexity of achieving compliance and navigate the process seamlessly. With Pondurance, organizations can rest assured they are not only meeting compliance standards today but also prepared for tomorrow’s ever-evolving threats.
In wrapping up, developing a robust cybersecurity strategy involves understanding the components of a cybersecurity strategy, cybersecurity compliance, and tailoring solutions to the organization’s specific requirements. To effectively safeguard against a myriad of cyber threats, a multi-layered approach featuring a Security Operations Center (SOC), compliance initiatives, an incident response plan, and leveraging managed services is crucial. This comprehensive and adaptive strategy not only addresses current challenges but also ensures resilience in the face of evolving cyber risks. By integrating these vital elements, organizations can fortify their defenses and navigate the complex cybersecurity landscape with confidence.