Developing an IR Plan To Defend Against Cyberattacks
Pondurance December 06, 2021
U.S. companies have seen an increasing number of ransomware attacks in 2020 and 2021, including the SolarWinds, Colonial Pipeline, and JBS Foods attacks, leaving companies of every size and industry concerned that they are vulnerable. And that concern is justified. A survey by International Data Corp. showed that more than one-third of companies worldwide had been hit by one or more ransomware attacks in the previous year. With odds like that, what should a company do to protect itself from being the next victim of a cyberattack?
Developing an incident response (IR) plan is a smart place to start. But what is an incident response plan? Our Incident Response Planning eBook offers a clear, straightforward explanation that answers many questions you may have about implementing a comprehensive IR plan to defend against a cyberattack. The eBook covers key points including:
What is an Incident Response plan?
An IR plan is a set of instructions that can be implemented through a third party or on your own to prepare your company to respond to a cyberattack. In the eBook, you’ll learn the baseline considerations for how to handle cyber incidents and the questions you’ll need to answer in the event of an attack.
How to create an IR plan
Companies should consider three main components when outlining an IR plan, including proper inventory, ongoing review, and training. In particular, companies that handle sensitive information, such as personally identifiable information and financial data, tend to be targets for cyberattackers, so it’s important to know the vulnerable entry points in the network and where the sensitive data resides. Also, the IR plan should be continually reviewed and audited, and all departments within the company should be trained and prepared for a cyberattack.
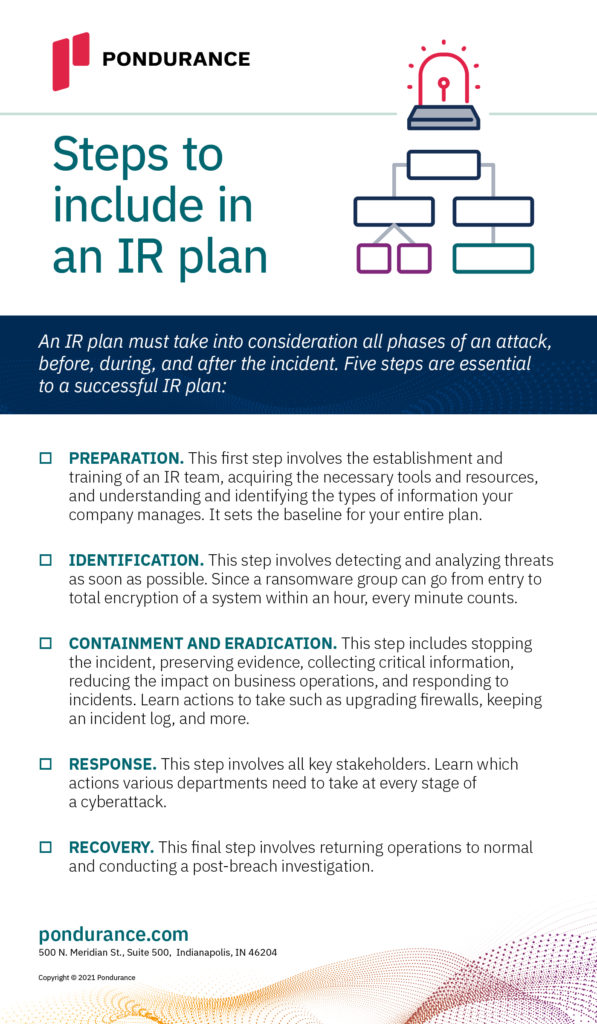
Steps to include in your IR plan
An IR plan must take into consideration all phases of an attack, before, during, and after the incident. Five steps are essential to a successful IR plan:
- Preparation. This first step involves establishment and training of an IR team, acquiring the necessary tools and resources, and understanding and identifying the types of information your company manages. It sets the baseline for your entire plan.
- Identification. This step involves detecting and analyzing threats as soon as possible. Since a ransomware group can go from entry to total encryption of a system within an hour, every minute counts.
- Containment and eradication. This step includes stopping the incident, preserving evidence, collecting critical information, reducing the impact on business operations, and responding to incidents. Learn actions to take such as upgrading firewalls, keeping an incident log, and more.
- Response. This step involves all key stakeholders. Learn which actions various departments need to take at every stage of a cyberattack.
-
Recovery. This final step involves returning operations to normal and conducting a post-breach investigation.